This is the fifth part of a seven-part series explaining and setting up a two-tier PKI with Windows Server 2016 in an enterprise SMB setting.
*Note* (16 May 2017): This page is currently in progress, is unfinished, and likely contains errors. I published it in this state due to time constraints, and will be working on it over the next week until it’s finished.
Because of the long time period between part 4 and part 5, I had to recreate my demonstration lab. Everything is functionally the same, but you may notice some different IPs or other minor changes.
Part 1 (Informational)
Part 2 (Getting Started & IIS Web Server Configuration)
Part 3 (Standalone Offline Root CA Configuration)
Part 4 (Enterprise CA Configuration)
>>> Part 5 (Distributing Certificates & AutoEnrollment) <<<
Part 6 (Additional Configuration)
Part 7 (Troubleshooting & Clean-up)
To help with the layout and navigation of these longer pages, use the Table of Contents below:
Certificate Templates
Now that you have the IIS, Root CA, and Enterprise CA servers basically set up, it’s time to create or distribute certificates to users and devices. But, before we can do that, we must create the templates from which the certificates will be made.
There’s a ton of reasons you would want to distribute user and computer certificates, and a ton of certificate templates you could configure. To name a few popular examples, you could have a template for the following purposes:
- Web Server SSL certificates
- Email S/MIME certificates for digital signatures and encryption
- One for digital signatures
- One for encryption
- Smartcards
- IPSec
- File encryption
- …etc
If you are a small or even medium size business, require a simple PKI, and don’t want to deal with the extra administration of multiple certificates, you could combine them a little if you are using strong encryption algorithms. This of course depends on a number of factors, so don’t just go ahead and do it…
For example, lets say that due to new email security concerns, you need to require that all emails from company users are digitally signed and encrypted. You could do that with a single certificate. Best practice may suggest that you use separate certificates; one for digital signatures, and one for email encryption. You don’t have to. Will it matter? Not likely, but it can.
However, your company may have legal reasons to do so, and may be required to separate them! You may also be high-risk. Always find out first! The main reason for separating them is to spread risk. If your encryption key was compromised, not only could the attacker decrypt your emails, but they could also impersonate you by using the same key to digitally sign emails as you! The same idea goes for whatever else the certificate is used for. Another two reasons, are that you may also want to set certain certificates to expire sooner or later than others… or for archival (escrow) purposes. There are definitely other reasons, but for now you get my point.
For the purpose of keeping this guide simple and still useful, I’ll guide you through creating a single template for email (digital signatures and encryption) certificates, and a template for one-off Web Server SSL certificates. Once you can do these, you can easily make and distribute certificates for any purpose, such as those listed a bit above.
Creating your (S/MIME) Certificate Template
On the server issuingCA, we will duplicate a preexisting user certificate template and configure it to our needs for digitally signing and encrypting email.
Duplicate a user certificate template
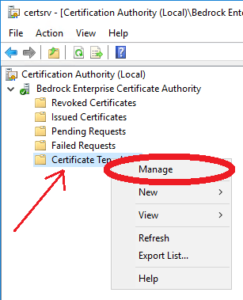
- Open up Certification Authority manager.
- Right-click on Certificate Templates and select Manage.
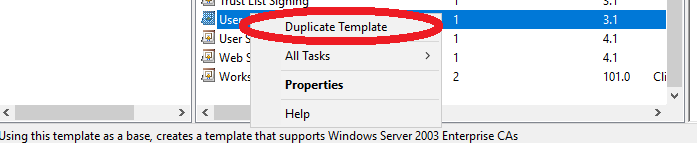
- Right-click on the User template and click Duplicate Template.
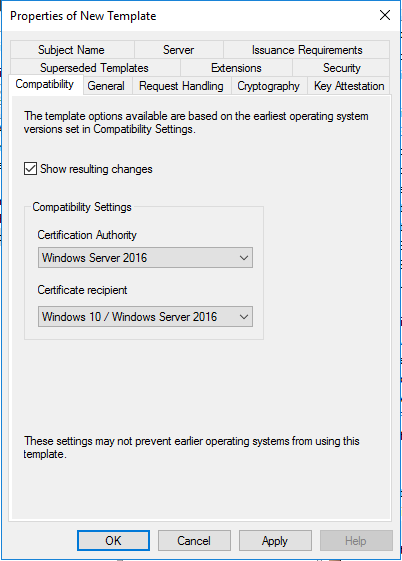
- In the Compatibility tab, select your appropriate compatibility levels.
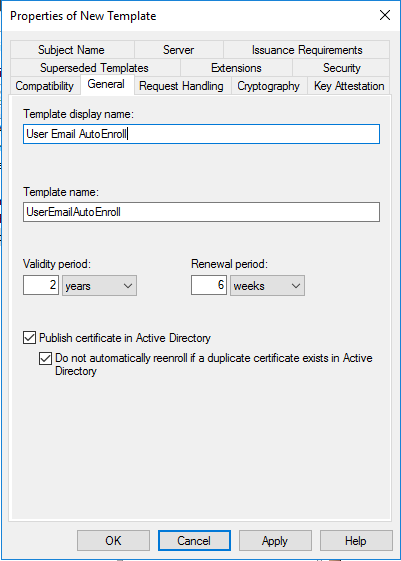
- In the General tab:
- Type a display name for your new template.
- Set a validity period. Two years is a good standard that meets most usage requirements.
- Renewal period sets the amount of time before the validity period expires in which the certificate will be renewed. Six weeks is sufficient for a two year validity period.
- CHECK Publish certificates in Active Directory.
- CHECK Do not automatically reenroll if a duplicate certificate exists in Active Directory.
- Some reasons you want this enabled is in the case users will log on to more than a single computer, and if you don’t want users to keep getting multiple certificates via auto-enrollment.
- If the certificates are stored in AD, we’ll be setting a Group Policy to have their certificates automatically “follow” the user no matter which computer they log on to in the domain.
- In the Request Handling tab:
- CHECK Archive subject’s encryption private key.
- We’ll be enabling key archiving later, before we start distributing certificates with this template. You may or may not want to do this in your production environment due to policies or legal reasons. Check first! Generally, it should be okay, and is nice to be able to recover a users private key in the case it is lost.
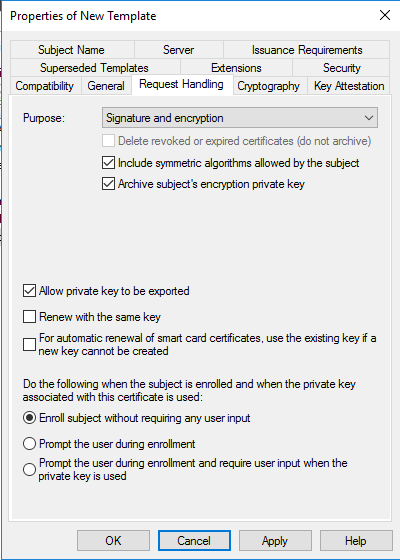
- We’ll be enabling key archiving later, before we start distributing certificates with this template. You may or may not want to do this in your production environment due to policies or legal reasons. Check first! Generally, it should be okay, and is nice to be able to recover a users private key in the case it is lost.
- CHECK Archive subject’s encryption private key.
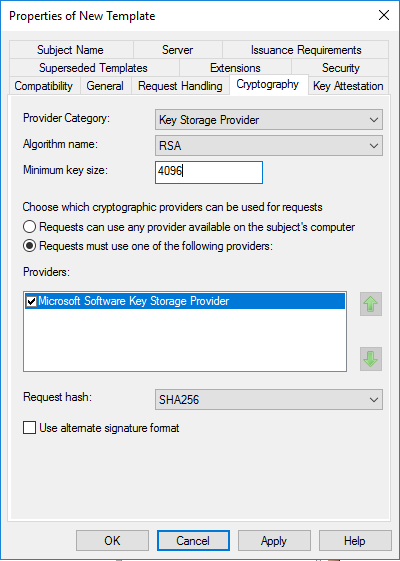
- In the Cryptography tab:
- Provider Category, select Key Storage Provider.
- Algorithm name, verify RSA is selected.
- Minimum key size, change it to 4096.
- Select Requests must use one of the following providers:
- Select Microsoft Software Key Storage Provider
- Request hash, select SHA256. Legacy clients may not work with SHA256 and may require updates, or your environment may need CSP. Check first.
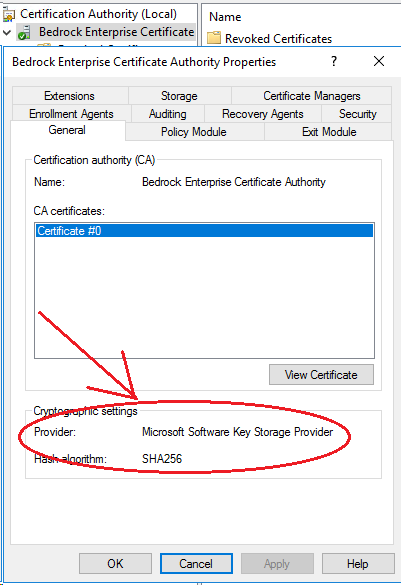
- Note that this area may be greyed out. You should be using Key Storage Provider. You can check what is used in the CA Properties here:
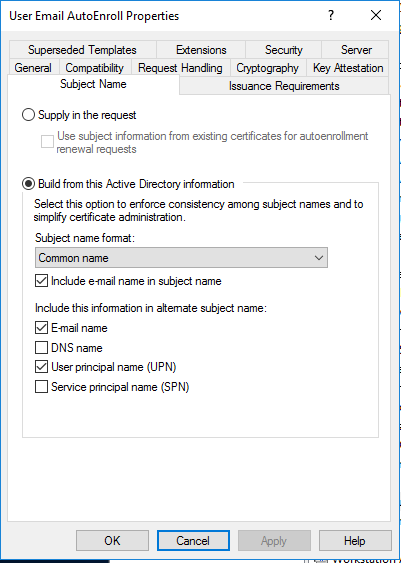
- In the Subject Name tab:
- In the Extensions tab:
- In the Security tab:
- Select each user/group at the top and verify the following are checked:
- If there are any users in the domain you do not want to have autoenrolled, you can create a group in Active Directory, add the user(s) to it, then add that group in the Security tab above, checking the Deny box for Autoenroll for that group.
- Click Apply, then click OK.
Publishing your (S/MIME) Certificate Template
Publishing a certificate template makes it available for use. To publish your above S/MIME certificate template (or any other certificate template), follow the below steps.
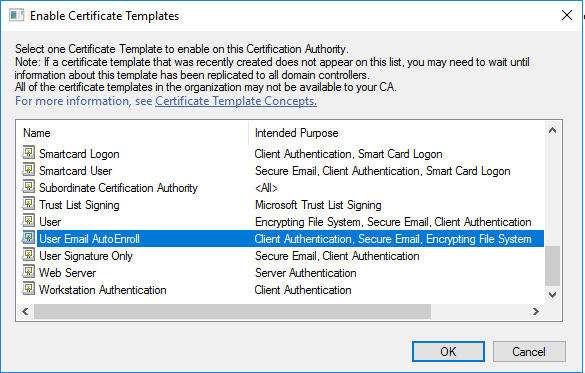
- In Certificate Authority manager, click on Certificate Templates.
- Then right-click Certificate Template, go to New, and click Certificate Template to Issue.
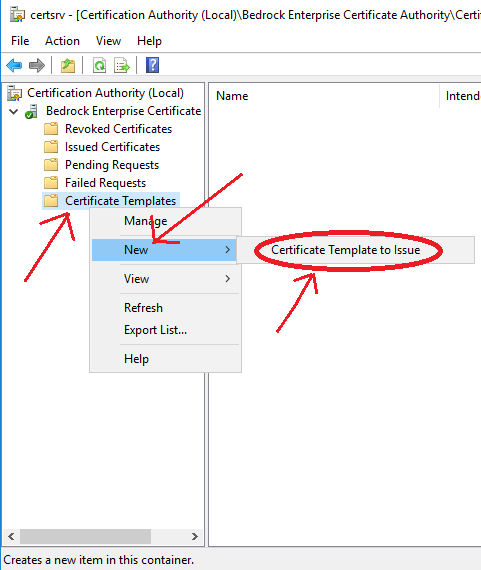
- Scroll down to find the template you created: User Email AutoEnroll, and click OK.
- asdf
Autoenrollment will not automatically hand out certificates to users until we create and configure a GPO that is distributed to all domain computers. But before we do that, we need to enable private key archiving.
… article in progress …





Hello. I got error: https://social.technet.microsoft.com/Forums/getfile/1552877
I found that this error is related to the key “Archive subject’s encryption private key”
https://social.technet.microsoft.com/Forums/getfile/1552908
What the problem and how i can fix it ?
Hi Tim,
I have followed everything on this blog. However, I am short on the Webserver to where it involves certsrv and certenroll cause obviously the requested cannot do the url because the steps on creating this isn’t there on the blog yet. I understand this is NOT your problem but I kinda have a due date to where i need to finish the CA servers. Is there anyway you can guide me through the last piece of the configurations with regards to the Webserver? Perhaps a peek on your write up? You can send to . Thank you o much. I appreciate it. Bob
Did you ever update Part 5, or finish Parts 6 and 7? Using your guide to deploy a new SHA-2 hierarchy to replace a SHA-1. Thank you.
Hi Timothy,
Fantastic series so far! Any ETA on when you’ll be able to continue?
Thanks,
Corey
I am not sure when I will have the time to create a new environment and finish the series. I want to soon, but it will require more time than I have to set everything up again.
Great guide! Any chance you’ll complete the last two sections? Thanks so much for your time to write these up!
This guide has been a huge help I too would love to see this completed.
This is literally one of the best guides out there.
Any idea when parts 6 and 7 will be completed?
I have installed a two tier PKI environment on server 2016 in parallel to our existing 2008
I went into PKIVIEW.MSC on the issuing CA to perform a health check, On the Enterprise PKI – I right clicked Manage AD containers, I cannot find an entry for my New Certificate Server under “CDP Container” tab (old servers are there with base and delta CRL) and also the KRA container is empty.
In the active directory sites and services under Services->Public Key Services->CDP; I can see the new issuing CA folder and inside the folder the new CA name listed as cRLDistributionPoint. Under KRA tab the new CA name is listed as type msPKI-PrivateKeyRecoveryAgent.
Is this normal or am I missing something? If I am missing something how do I fix it.
You wont see your CA on that list unless you took the steps to publish the CRL to your Active Directory. If you’re following this guide the steps are there but are recommended to be skipped.
Thanks for the excellent guide. Do you have any timeline for completing the rest of it ?
Hi, thank you for your hard work in getting this series going. I was planning on using this guide to deploy PKI, Smart Cards and SSO but since the guide is incomplete I hesitate to follow it. It is now March 2019 do you have plans to complete this guide if not does anybody have any links to completed works?
Thank you
Excellent guide, I was following this guide to deploy now I am stuck, is there any article you can point me to complete my deployment? How do I setup the certsrv weblink to request certs? Is it on the webserv1 or the issuingCA? Please help.
Do you plan on finishing the guide?
Yours is the only walkthrough that is doing user enrollments and also https certs.
I’m hoping to try smart-card computer access at home, while also getting rid of the certificate errors accessing my various devices 😉
Yes I will soon.
*offers beer money* haha 🙂
Hi Timothy,
Thanks for the excellent guide.
As many of the others I’m looking forward to you finishing it.
Cheers
Thomas
Curious as to why you chose the KSP for provider on the user template duplication? If it’s not required to change to KSP for requests in order to support ECDSA certificates then I typically stick with CSP for provider. For one thing in order to use the CERTSRV page you cannot have certificates higher than version 2. While using KSP as provider will make the version 3 or higher and the certs will not be visible in CERTSRV.
I primarily ask because there is often confusion in regards to this setting having an effect on the certificate hash itself which it does not, it is only related to the request. I have had some clients who elected to set this and afterwards are asking why they cannot see the template on CERTSRV after publishing the template because of that confusion.
You’re right. In the example I provided, those certificates are used for AutoEnrollment and deployment via ADDS and are not needed via CERTSRV.
If you need certificates available via CERTSRV for other purposes, then of course you’d configure the template appropriately.
As always, with any guide, YMMV. Each environment should be evaluated and configured according to it’s own needs.
Guides like this are meant as a way to get started and not as a one-size-fits-all deployment.
I hope you will finish this great series of articles.
Very interesting…
Please put me in the class of people that would really love to see this completed.
Any change on getting the article finished!? It was excellent, but you gotta close it out.
Yes, thanks… I will soon.
I very much look forward to it. It was a very good read.
Thanks ever so much for your help so far, your guides are certainly some of the best that I have come across. I just wish i’d read through the whole guide and realised it wasn’t finished before I starting my deployment. Might be worth putting a note at the top of the first page to explain that the guide isnt finished before other colleagues like myself start working through.
Thanks again.
Very good guide. Thank you. Waiting for next parts.
I have been using this guide to deploy a PKI at my workplace, and have hit the point where the guide stops. I am trying to read up on what could possibly be my next steps, but I have one question. The web enrollment & online responder roles will need to be installed on the Issuing CA or the webserver?
No part 6 or 7. Not really complaining as the existing entries are excellent material but I was really looking forward to the “Troubleshooting and Clean-up” section.
I’ll get to it soon! The next 2 weeks will be too busy to dive back into that, but afterwards I plan on completing it.
Timothy, I fervently hope that you will be finishing this fine series. I have been following it and setting up a PKI for my firm but I’m not quite ready to commit until I get the final 3 parts from you. Please find time to finish this fantastic guide
I will, I promise, as soon as I have time. Things are a bit busy at the moment. I need to rebuild a lab to finish it out for the purpose of these articles. It’s just a matter of finding the time. I hope to sometime in the next few weeks to a month.
Timothy, your guide is the best. Please do. The world will owe you a favor.
Hi Timothy, this guide has been a great healp in setting up a PKI in my homelab environment. Just curious, is there a change you’ll finish up part 6 and 7?
Thanks for the great guide. I look forward to seeing it finished!
Please finish the rest of the guide. I am using it for a different purpose other than S/MIME but have adapted it to my environment. It has been extremely helpful. There are lots of things left unanswered. Like the remaining IIS configuration which is crucial. It was extremely disappointing to see this is where the guide ended.
Which part of the IIS configuration are you stuck on?
at the end of part 2 you say:
Additional Configuration
There are still some more configurations to be done on this web server, but we can’t do those until the RootCA and EnterpriseCA are set up and configured. For example, we can’t set up “CertSrv” on here yet, because that requires an Enterprise (subordinate issuing) CA.
These things will be configured in later parts of this series.
That is what I’m missing to finish the setup
The RootCA and EnterpriseCA are done in parts 3 and 4, so after that you will be able to set up CertSrv.
Hi,
Good work on the series so far. Is there any chance that the series or even just this part could be published.
I would like to get my new CA environment fully deployed,
Thanks
Any chance that we will see the remaining parts in this series published? I’m stuck on the templates part – I just am unsure as to what to do next. I am not at all a PKI wizard.
Just wanted to say thanks. This is definitely the best/most modern article on the topic. In the past I have had to use a complication of Technet & 3rd party articles to piece together a functional PKI deployment.
Hello Timothy,
I’ve been eagerly awaiting your return to this topic. Any chance of finishing it off in the near future?
This is the greatest help i’ve found. Thank you for your time and effort in sharing your experience with this.
I’m planning a CA implementation and have found your documentation to be the best.
This is some quality documentation!! Do you have part 6 and 7 ready? I’ve followed up until part 5 and now I’m not sure what comes next or of I’ve missed something. This has taken an incredibly complex process and made it much easier to understand. Thank you!
Thank you! Sorry for the delay.
See my comment here: https://www.timothygruber.com/pki/deploy-a-pki-on-windows-server-2016-part-5/#comment-853
This guide has been an AMAZING help! Do you have any plans to complete parts 6 & 7 (and list part 5 as complete)? And possibly the OCSP section? I for one, appreciate all the work you have put into this guide so far.
Thank you! Yes I do plan on finishing the whole series. I’ve just been very busy lately, my lab for this series expired, and will need to find the time to set it all back up again to continue where I left off.
I will try to get it finished soon! Sorry for wait.
I have a few scripts that I’ve written to automate the lab rebuild process. If you want them, you can find me at the email I’ve used here.
This has been a GREAT guide. I’ve been putting this project off for years and now have implemented a proper CA in my network. Any chance you could post a quick and dirty outline of the next steps. I’ve deployed as far as you’ve posted and its working so far I just want to make sure the parts that I’ve filled in aren’t completely wrong.
Hi Thomas ,
Thanks so.much although I now have a root ca and and enterprise issuing server . I am a bit stumped on setting up ocsp . And on where that should sit ? I initially started this to do WiFi and VPN securely . With a pretence of implementing Azure AD in the near future. Hoping you are able to finish this soon . Thanks for the help so far
Hi Timothy, great content!
I am setting up in a home lab to learn this myself and have enjoyed the guide thus far.
Any chance you may have time/motivation to continue please 🙂
Looking forward to it.
Cheers again,
Mario
Great Post!! Would you mind sharing your references so we can attempt to complete the configuration on our own?
Appreciate the time and work it takes to document the process with lots of explnations on why it was configured this way.
Looking forward to the info on deployment – there seems to be nothing out there for 2016 that is complete.
Hi Timothy
is there any reason the certificate enrollment service is not installed on the web server? could you list what other task should be done (no detail im sure you are very busy.
Thanks
Your Step by Step Guide is one of the most complete and detailed guides that I know, it is very helpfull. It will be sad if it is not complete
Where’s the rest of part 5? The first 4 parts were great and very detailed.
I have been busy abroad and haven’t had time to finish it yet. Hopefully the end of August.
Thank you for posting such detailed directions! It has been a great help in rebuilding my PKI.
Just wanted to say thanks for the excellent walk through. I know this took time to do, and it’s an incredible help for building a CA environment on Server 2016, for which there is little updated documentation.
Thank you.